Cue Health’s at-home COVID-19 testing kit contains a fault that might let users to fake findings, according to a security researcher. The COVID-19 testing kit from Cue Health is a Bluetooth-enabled molecular test that may identify positive samples in as little as 20 minutes. The device uses a nasal swab put into a single-use cartridge to test for coronavirus, which is then processed by the battery-powered Cue Reader, which subsequently sends the results to the test-phone takers through Bluetooth. Cue’s method was the first molecular COVID-19 testing kit to get emergency FDA approval for at-home and over-the-counter usage in March 2021.
While the FDA praised Cue Health’s unique approach to COVID-19 testing at the time, Ken Gannon, a security expert at WithSecure, F-corporate Secure’s security division, discovered a weakness in the kit that might allow test results to be tampered with. The same researcher who previously uncovered a similar problem in Ellume’s COVID-19 Home Test has identified a security vulnerability in a linked COVID-19 test, bringing into doubt the integrity of testing kits rushed to market under the federal government’s emergency approval powers.
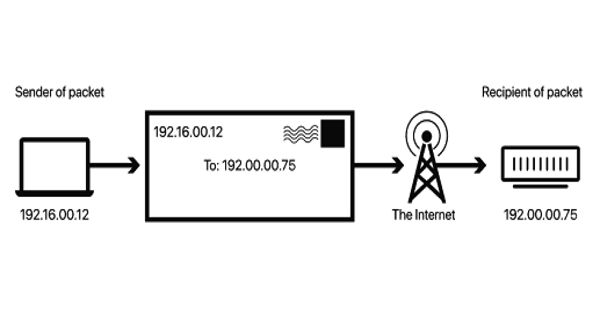
The flaw was discovered in the way the Cue Reader communicates with the Cue Health app through Bluetooth utilizing the Protobuf protocol, which provides the test data in a readable block of data. For a positive COVID-19 test result, the Reader’s data block finishes in “10 02,” while for a negative result, it ends in “10 03.” Gannon created software that allowed him to intercept and manipulate data using these numbers. Gannon may transform his negative result into a positive result and receive a certificate validating the results as authentic by changing a single number in the result, or “bit-flipping.”
“The technique is virtually the same for turning a good result into a negative,” Gannon explained. “This might pose difficulties if someone who understands how to accomplish what I did starts faking findings.” COVID-19 tests that are negative are now required for various activities, including travel into the United States. “The expertise level necessary to flip those bits right now is fairly high,” Gannon added. “An individual would require some experience hacking mobile applications and executing custom code into Cue’s application.”